
COVID-19 Relief Efforts at PS1
While we remain closed in compliance with the Illinois stay-at-home order, a small and dedicated team of volunteers has

While we remain closed in compliance with the Illinois stay-at-home order, a small and dedicated team of volunteers has
We are fermenting up a tasty frothy storm over here in the PS1 kitchen! We have about 10 gallons
We’re excited to welcome CHI PRC’s Zine Zine Club Thursday 2/21 from 7-9pm in the lounge. We’ll be discussing DIY
Good news for Starving Hacker tier members: you can now vote at PS1 member meetings for things like purchases,
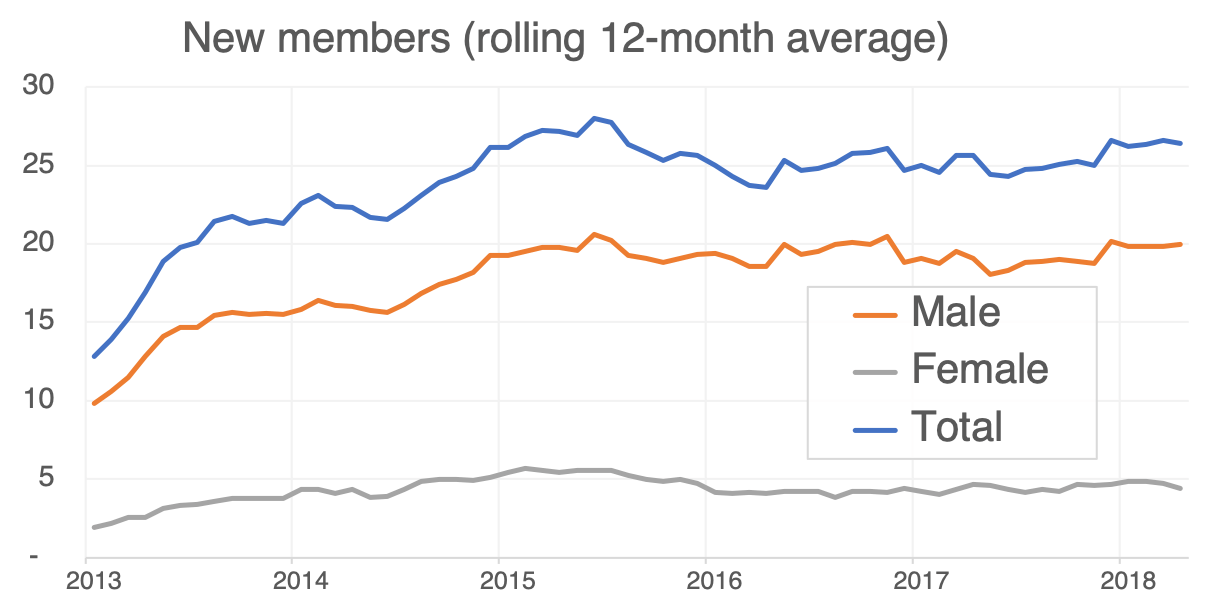
I used historical payment records to analyze member growth and member churn, the rates at which people join and
Update: great event! A recording is available here. All are encouraged to attend the candidate Q&A at PS1 on
In August, PS1 conducted its first-ever member survey to better find out who we are, how we use the
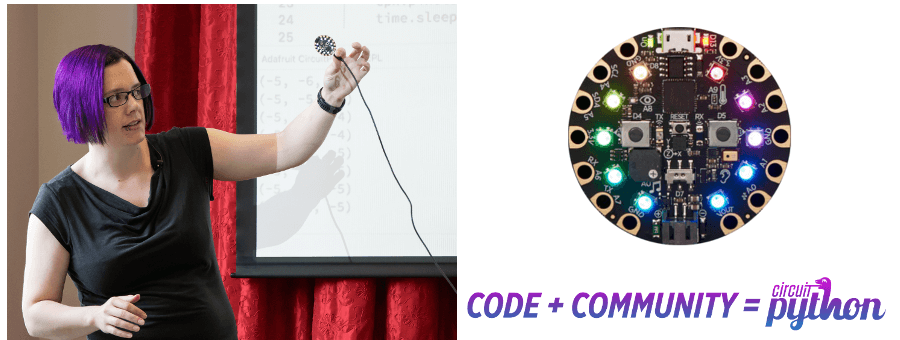
NERP (Not Exclusively Raspberry Pi) is PS1’s embedded programming interest group. At a special NERP on December 17, Kattni
PS1 will be holding annual board elections on January 15, 2019. Board elections affect everyone in the organization, whether